-
About NXON AI

NXON AI integrates smart cameras, embedded systems, and edge AI to enable real-time vision analytics at scale.
-
What we do

Engineering intelligent monitoring and automation solutions using AI, IoT, and embedded technologies.
-
Engineering Solutions
Cameras & Sensors
Network Video Recorders
AI VMS Platform
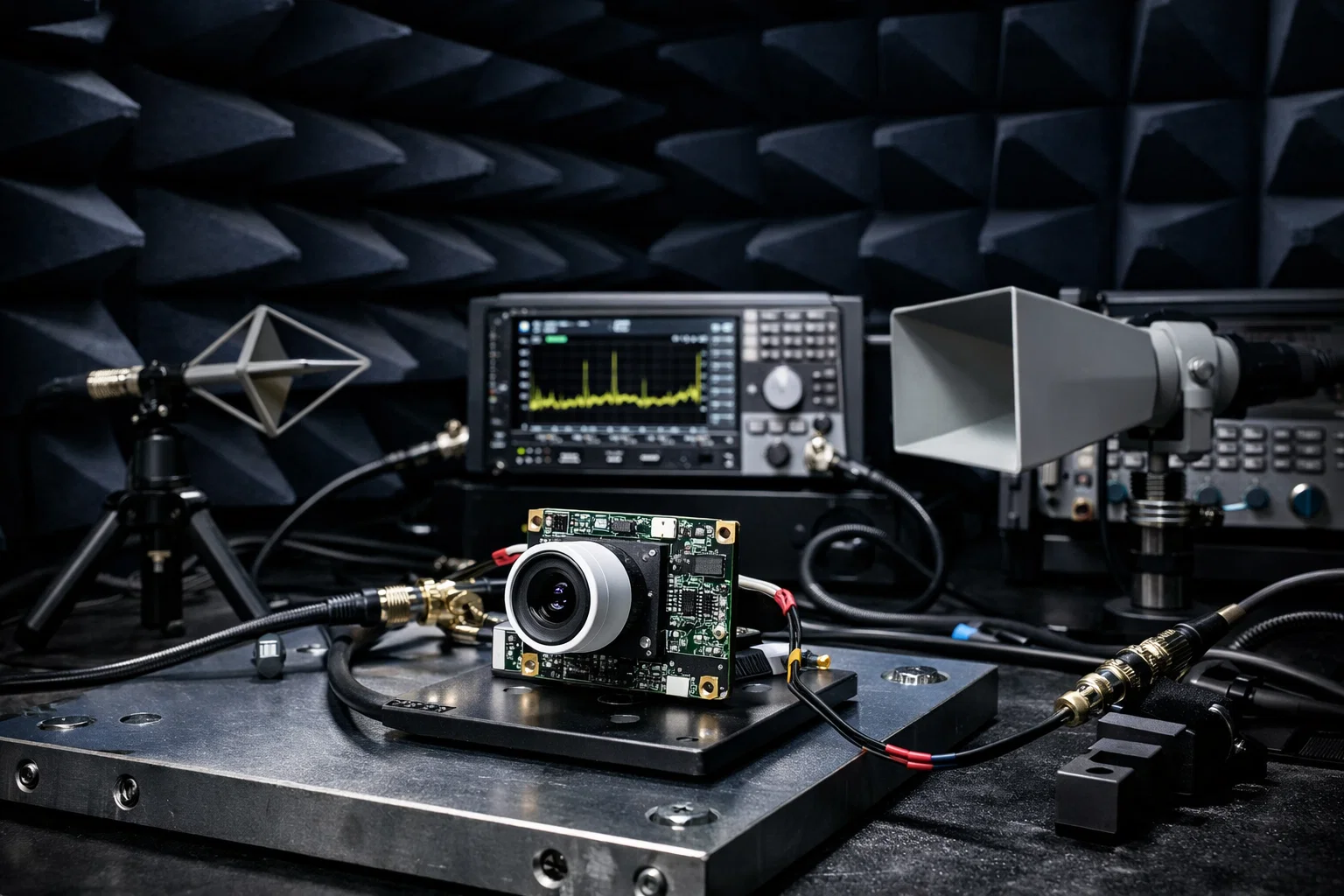
Vision & Edge AI

-
Industry

Intelligent edge-powered surveillance for safer cities and businesses.
- Perspectives
- News
- About NXON AI
- What We Do
-
Engineering Solutions
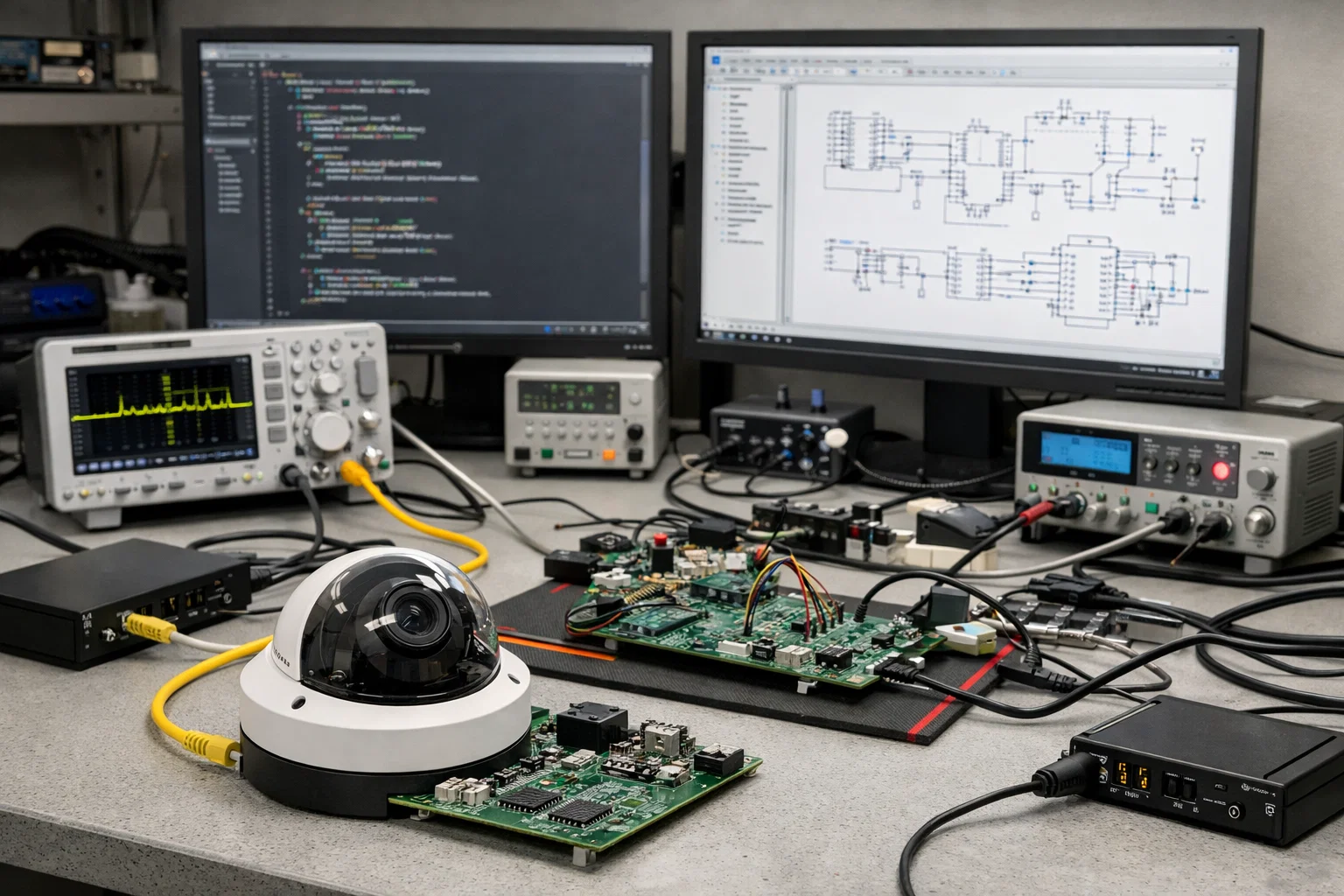
- Cameras & Sensors
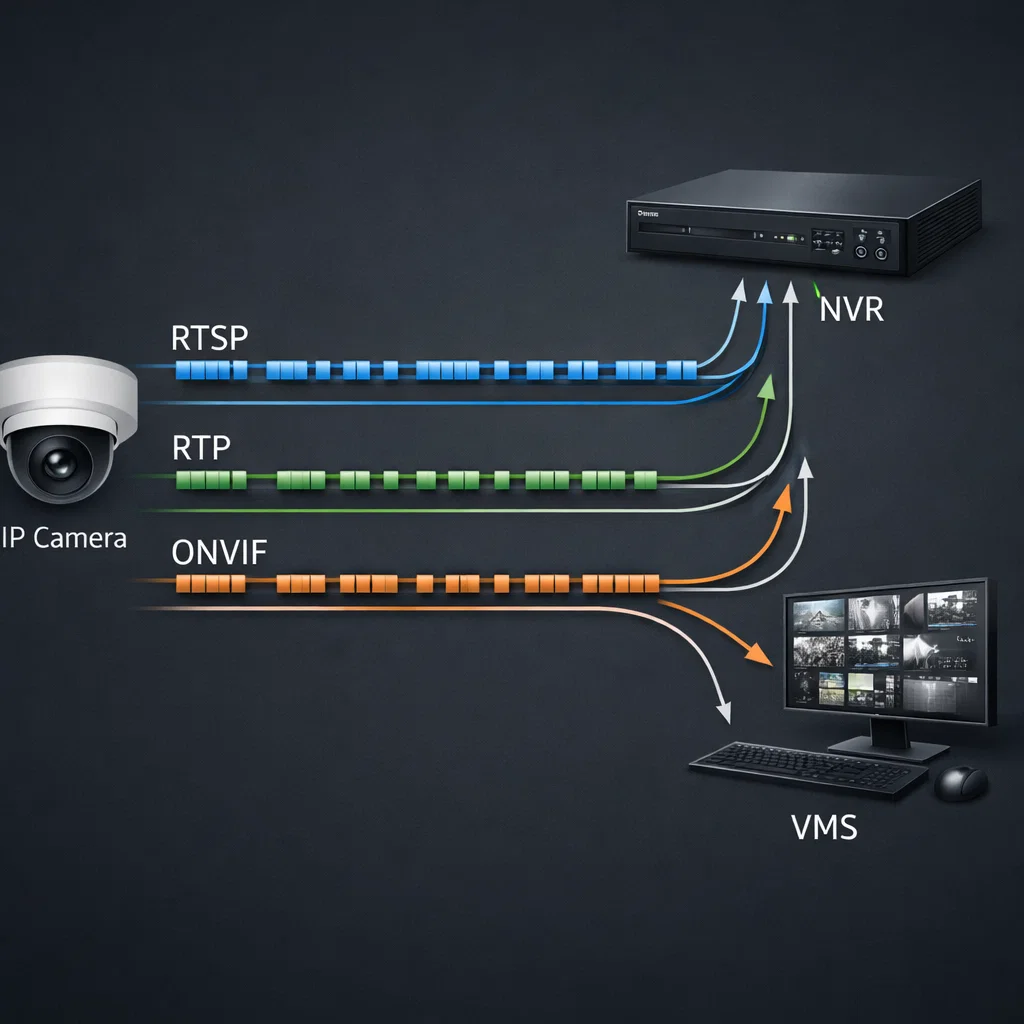
- Network Video Recorders
- AI VMS Platform
- Vision & Edge AI
- All Products
- Industry
- Perspectives
- News
Cameras & Sensors
Network Video Recorders
AI VMS Platform
Vision & Edge AI
All Products
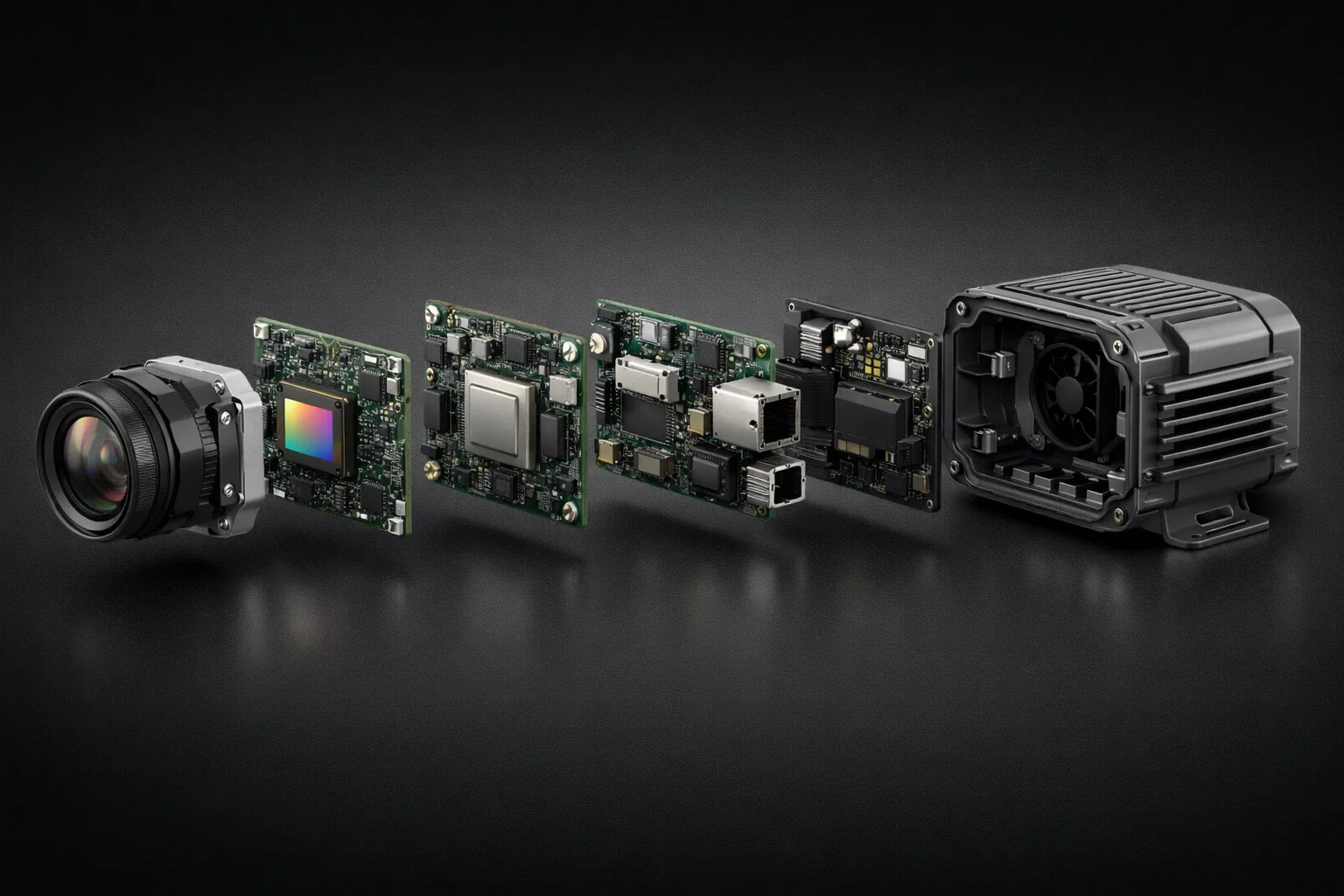
Camera Hardware
Edge Devices
VMS Software